Week 4 – Advanced Windows Security Course
Happy New Year to you all, 2017 is here! I’m spending the first week of 2017 catching up on the 4th week of course work… So far we have covered
- Windows 10/Windows Server 2016 – Platform Security and Internals
- Attacks on Credentials & Prevention Solutions
- Attacking & Securing Windows Network
- Handling Ransomware & Other Malicious Software
- Implementing Security Policy Settings
- Offline Access – Threats and Prevention
This week we are going to cover
Providing Data Security and Availability
High Availability
Round Robin
Uses DNS to provide a basic form of load balancing and failover (failover requires the application to try each IP returned by the DNS query) You simply create multiple A records with the same DNS name. DNS can’t detect if a server is down or degraded.
Network Load Balancing (NLB)
Windows provides a software load balancer to provide load balancing and failover capabilities. NLB uses heartbeating to ensure that the servers in the NLB cluster are running. It cannot detect a degraded service though, only a total node down.
Hardware Load Balancing (HLB)
Third Party appliances can provide comprehensive load balancing features including probes to check if the nodes are up/down or degraded and take appropriate action. HLB devices are sometimes categorized as Layer-3 and Layer-7 devices. This refers to the ISO stack for networking which has 7 layers. Layer-3 simply means it understands IP addresses and ports but that is pretty much it. Layer-7 devices can understand the applications themselves, e.g. http, https and smtp to perform deeper inspection and more complicated load balancing rules. Most software that can require load balancing these days relies on layer 3 load balancing as a minimum requirement. Older technologies such as Exchange 2010 and earlier needed Layer-7 load balancers with more complex rules.
Failover Clustering
- Cluster Operating System Rolling Upgrade (only intended for short-term state say 30 days)
- Clusters now have functional levels (2012 R2 and 2016 at this time)
- New 2016 nodes can be added to a 2012 R2 Cluster
- Once all 2012 R2 servers have been removed from the 2012 R2 Cluster then the cluster functional level can be raised to 2016
- Workgroup and Multi-Domain clusters are supported
- Hyper-V will start even if part of a domain and no domain controller is available
- Hyper-V cluster nodes can continue to serve Virtual Machines even when it loses communication with the cluster (if on SMB3 storage)
- Hyper-V cluster nodes can be quarantined to allow them to be gracefully removed from the cluster
- Storage resiliency has been improved to avoid the Hyper-V cluster totally failing when shared storage is lost, instead it pauses the VMs and resumes them when the issue is fixed
- Site aware clusters allow you to specify which AD site a cluster node is in (better placement of VMs, more efficient quorum management and heartbeating
- Cloud witness to allow the witness to be in Azure
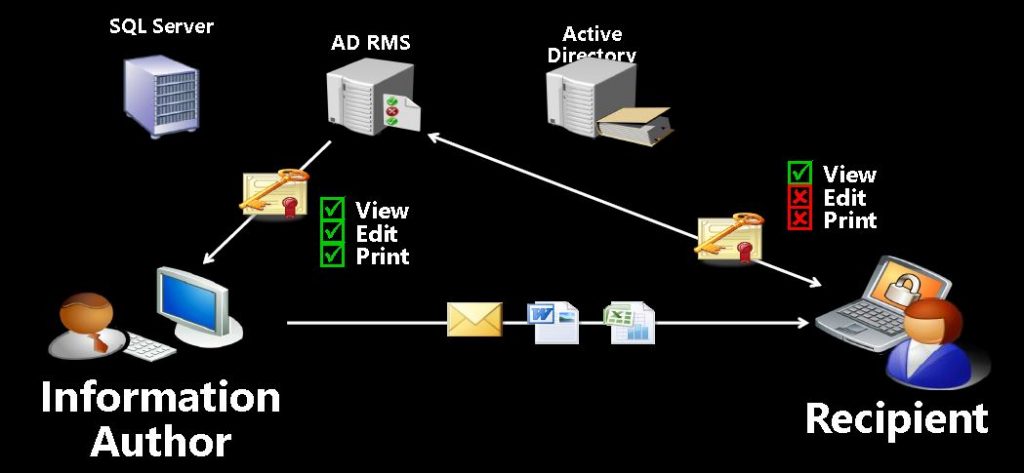
Rights Management Service (RMS)
Overview
- Information Protection Technology, aimed at reducing information leakage, also called Information Rights Management (IRM)
- Integrated with Windows, Office, Exchange, SharePoint, PDF, etc.
- Usage rights and symmetric keys stored in the file as a licence
- License is protected by a customer owned RSA key
- Each file is protected by a unique AES symmetric key
Logical View
AD RMS and SharePoint
- When content is downloaded from a library
- RMS protection is automatically applied if configured to do so
- Information is still searchable in SharePoint library
- SharePoint rights implies IRM permissions
AD RMS and Exchange
- Exchange Transport Rules and Outlook Protection Rules can apply protection automatically
- Rules can be based on the content (what it says) and the context (who it is going to)
- Protected mail can be consumed in Outlook, IE, Safari and Firefox
AD RMS and File Shares
- Bulk Protection Tool secures all content in certain folders
- File Classification Infrastructure (FCI) can automate classification, RMS and move into SharePoint
AD RMS Topology
- Two roles: Certificate service and Licensing service
- 2.4GHz dual core x64 CPU with 4GB RAM can deliver just over 100 licenses per second
- Scales linearly up to 8 cores, after that adding servers may be simpler
- Exchange pre-licensing has quite a big impact since emails may have many recipients each requiring a license
Azure Rights Management
Azure Rights Management is basically RMS in the cloud. It provides the following:
- Safeguards sensitive information
- Provides persistent protection
- Closer management of usage rights and conditions
- Integrates rights management with Office 365
Enabling Azure Rights Management in Office 365
- In Office 365 admin portal, under service settings, enable Azure Rights Management
- In SharePoint admin center under settings enable the use of IRM
- IRM enable SharePoint document libraries and lists
- In Exchange Online Shell use the following to enable RMS in Exchange Online (the URL shown is for Europe, see here for more details)
Set-IRMConfiguration -RMSOnlineKeySharingLocation https://sp-rms.eu.aadrm.com/TenantManagement/ServicePartner.svc Import-RMSTrustedPublishingDomain -RMSOnline -Name "RMS Online" Set-IRMConfiguration -InternalLicensingEnabled $true
In Outlook Web Access you should now see Set Permission under the … menu when composing a new message
SQL Server Protection
You can undertake the following steps to better secure SQL Server
- Don’t use mixed-mode authentication (too easy to get sa password in brute force attack)
- Keep SQL Server patches up to date
- Ensure that the service account used to run SQL Server is NOT a privileged account
- Disable xp-cmdshell
Attacking and Securing IIS Web Server
Simplified IIS Architecture
- HTTP.SYS listens on port 80, 443 and works out which process needs to handle a given URL from the bindings
- WWWPS (World Wide Web Publishing Service) is the overall management and orchestration process
- W(P)AS (Windows Process Activation Service, Process is generally ommitted in registry, etc. Reads applicationHost.config and starts the appropriate worker)
- w3wp.exe (World Wide Web Worker Process, run as a given identity)
Managing IIS Security
Keep the server patching up to date
There are lots of vulnerabilities that are found periodically and you want to ensure that your server is protected against these as fast as possible
Why not run another web server?
Patching IIS is simple, just keep the server patches up to date and IIS is also patched
IIS has very few vulnerabilities nowadays
Compare this to Apache
So there have been 20 IIS vulnerabilities since 2008, and Apache in the 2016 alone had 103…
IIS has many levels of possible security configuration including:
- Authentication: By default IIS 8.0 uses Anonymous Authentication
- Authorization: Determines which resources a user can access
- Certificates: Provide a way to confirm the identity of a website
- ISAPI and GCI Restrictions: Allow dynamic content to run on a Web server
- SSL Settings: Encrypts data between a server and a client
- HTTP Filters: Restrict the types of HTTP requests that IIS allows
- Roles: Perform security-related operations on multiple users
- Trust Levels: Permissions granted by ASP.NET security policy (in config under .NET Trust Levels)
- Users: Define users to be associated with an application
Configuring IIS features for security
Minimal Installation
- Modules/Handlers can be removed if not needed
Manage IP and Domain Restrictions
- IP restrictions not really that useful since IP easily bypassed
- Domain restrictions also not really that useful, but worse as it takes a long time so subject to DDOS)
- Dynamic IP Restriction Settings (concurrent requests, Max Request in an interval)
Deploy Restrictive Authentication Types
- Forms Based Authentication or Windows Authentication (with NTLM removed)
Deploy HTTP Request Filtering
- Reject double-encoded requests
- Reject non-ASCII characters in requests
- Define hidden segments
- Define which file filters are allowed
- Define list of approved verbs
- Define list of sequences that IIS will reject
- Define request limits
Restrict Directory Browsing
Turn on Failed Request Tracing
- can also turn it on for 200 with a x second response time (yep second granularity sucks)
Application Pool Isolation
- Use an identity such as IIS AppPool\www.tralala.com
- Within Anonymous Authentication – set Application Pool Identity as the account to impersonate
Note that application pool passwords are very easy to decrypt. IIS relies 100% on security of the OS
appcmd.exe list apppool /text:*
Authorization Rules
- Used to authorize users to access applications using a set of approved HTTP verbs (GET, POST, etc.)
Encrypting Config Sections
- Settings within web.config are clear text, however you can encrypt them using
aspnet_regiis -pef "connectionStrings" c:\Website -prov DataProtectionConfigurationProvider
and then you can decypt them again using
aspnet_regiis -pdf "connectionStrings" c:\Website
Deploying Server Name Indication and Centralized SSL Certificate Support
- Standard Server Certificate Management loads/unloads certs on demand into memory
- Stores certificates on a share, uses name to recognize them
- User and passwords configured in Edit Centralized Certificates Settings
- Stored insecurely and password has to be the same
aspnet_regiis -px "iisWasKey" c:\text.xml -pri
Monitoring Web Server resources and performance
You can add custom fields to the IIS logs such as X-Forwarded-IP, or performance log counters
Deploying Distributed Denial of Service attack prevention
FTP Logon Attempt Restrictions
max failed login attempts in an interval